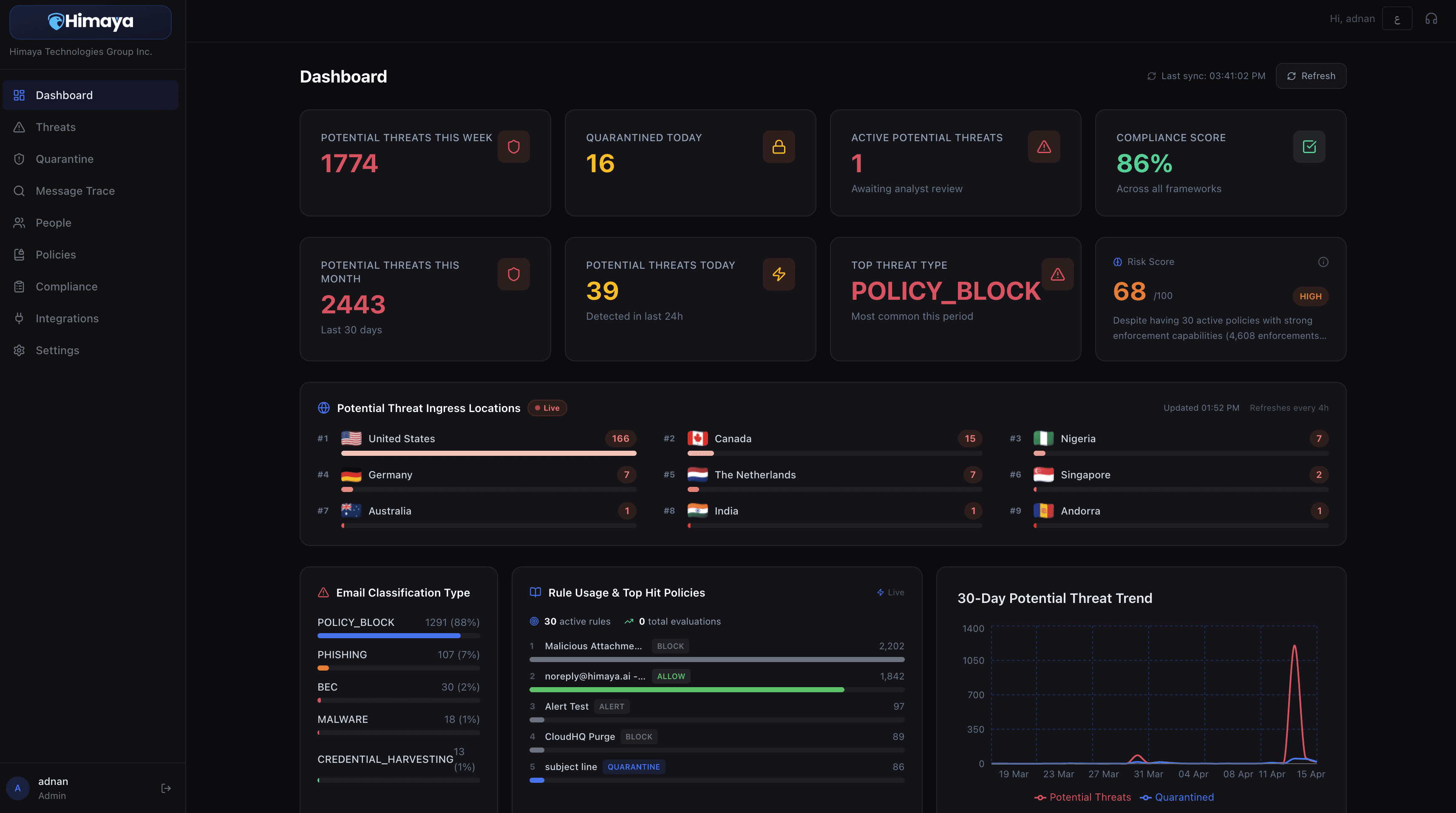
The Himaya Helios Platform
Leverage Himaya’s AI-native, agentic email security platform to detect, investigate, and remediate phishing, business email compromise, impersonation, and mailbox abuse with speed and clarity.

Agentic Security Engine
Link Analysis Agent
Inspects suspicious URLs, redirect chains, landing-page behavior, and domain risk signals to surface phishing intent before users click through.
Triage Agent
Reviews reported and detected emails, explains why a message is suspicious, correlates related signals, and helps analysts prioritize what needs action first.
Automation Agent
Executes guided response workflows such as quarantine, purge, forwarding-rule cleanup, user scoping, and escalation to accelerate containment.
Sync Agent
Continuously syncs messages, alerts, user-reported phishing submissions, policy updates, and response actions across connected email environments.
Transparent Pricing Plans
Launch
Self-service access to Helios with full platform capabilities.
$5
/ user / month
AI-Driven Email Classification
Automated Policy Enforcement
Email Sandbox Access
Compliance mapping & reports
Report Phish Add-on
Basic Support
Enterprise
Self-service access to Helios with enhanced platform capabilities.
$11
/ user / month
AI-Driven Email Classification
Automated Policy Enforcement
Email Sandbox Access
Compliance mapping & reports
Report Phish Add-on
Auto-triage
Adaptive Email DLP
Premium Support
Managed
Popular
Full "Enterprise" platform access plus dedicated support and managed operations.
$28
/ user / month
Everything in Enterprise
Dedicated account manager
Managed remediation support
Phishing Awareness Training & Simulation
24/7 On-call Support
24/7 On-call Email Triage SOC
Quarterly business reviews

Our commitment
Intelligent protection, measurable outcomes, and automated around-the-clock defense for your inbox.



